Enterprise-Grade Security and Compliance for Kubernetes
Security tools flag issues, but don’t show how they threaten your workloads. Devtron unifies scanning, policy enforcement, and access control so you lock down clusters before risks spread.

Powering Mission-Critical Kubernetes for Global Enterprises
The Hidden Risks in Kubernetes
In Kubernetes, mistakes multiply fast. One leaked secret, one misconfigured manifest, one unchecked image, and your cluster is exposed. Traditional tools catch pieces of the puzzle. But by the time you connect the dots, it’s too late. Security and compliance shouldn’t feel like firefighting or guesswork. You need a platform that helps you see, prevent, and respond, before the threat spreads.
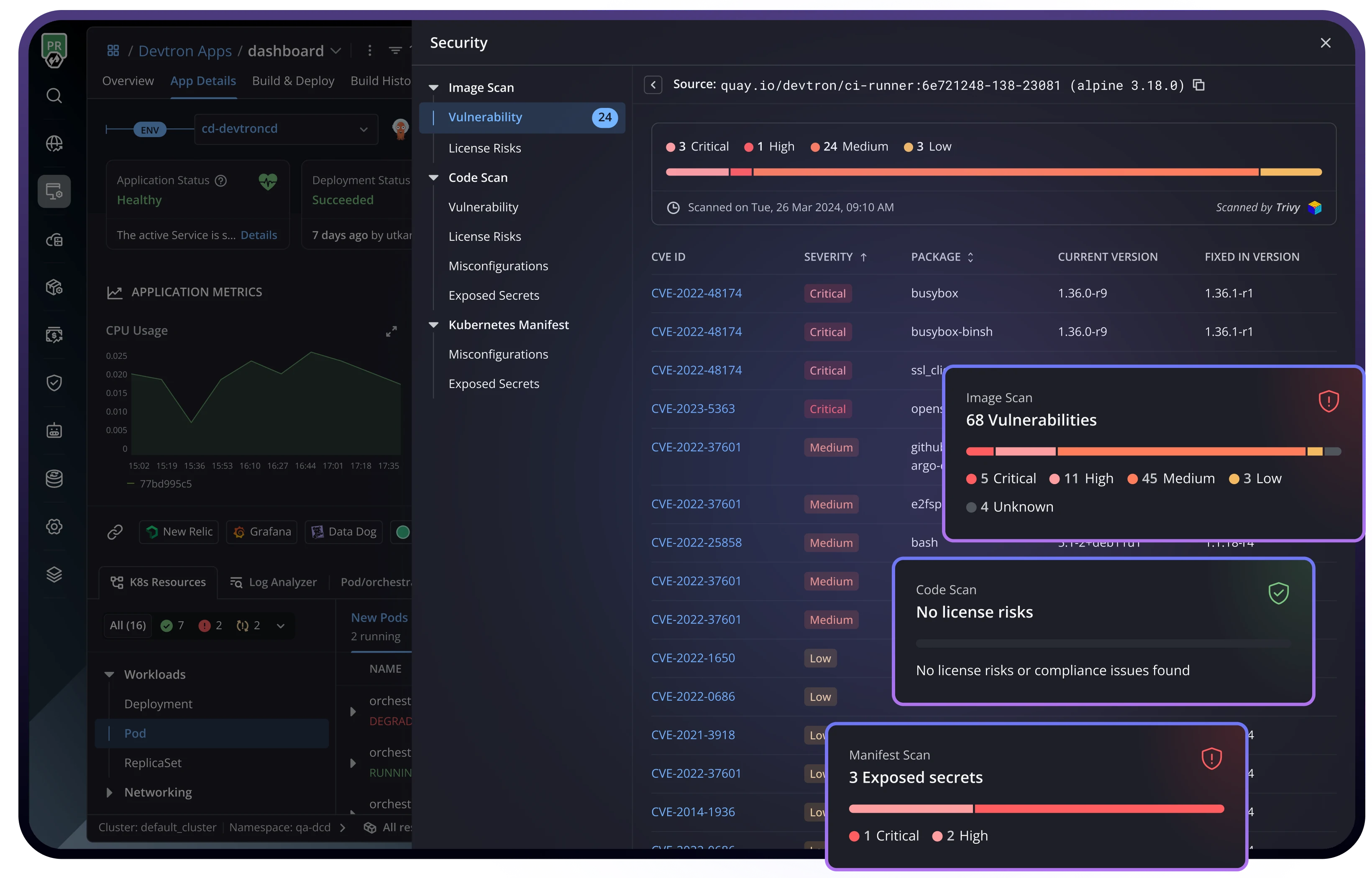
Automated compliance scanning
Security starts before code reaches the cluster.
Embed security into every stage of your workflows with Devtron’s compliance scanning.
Image Scanning
Detect issues in container images and base layers.
Manifest Scanning
Catch misconfigurations and security gaps in Kubernetes YAML.
Secret Detection
Expose leaked secrets in code and configurations.
License Scanning
Flag risky dependencies and licenses before shipping.
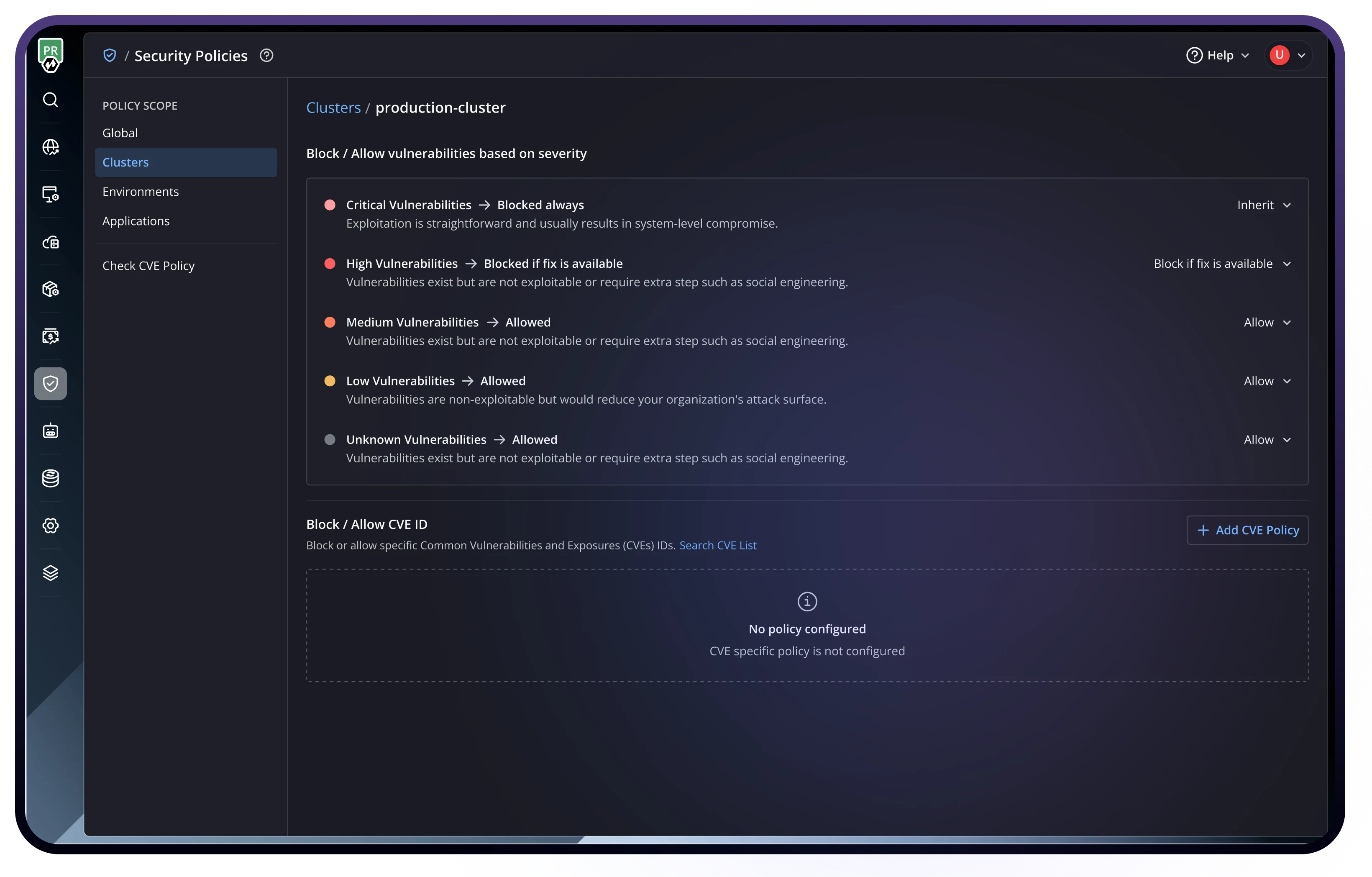
Intelligent Policy Enforcement
Turn security standards into enforcement, not suggestions.
Stop letting misconfigurations and vulnerabilities slip into production.
Multi-Level Policies
Set rules globally, per cluster, environment, or app.
Behavior-Driven Security
Create policies that match your real-world workflows.
Pass/Fail Conditions
Block pipeline progression based on severity levels.
Image Approval Workflows
Require sign-off before promoting images to prod.
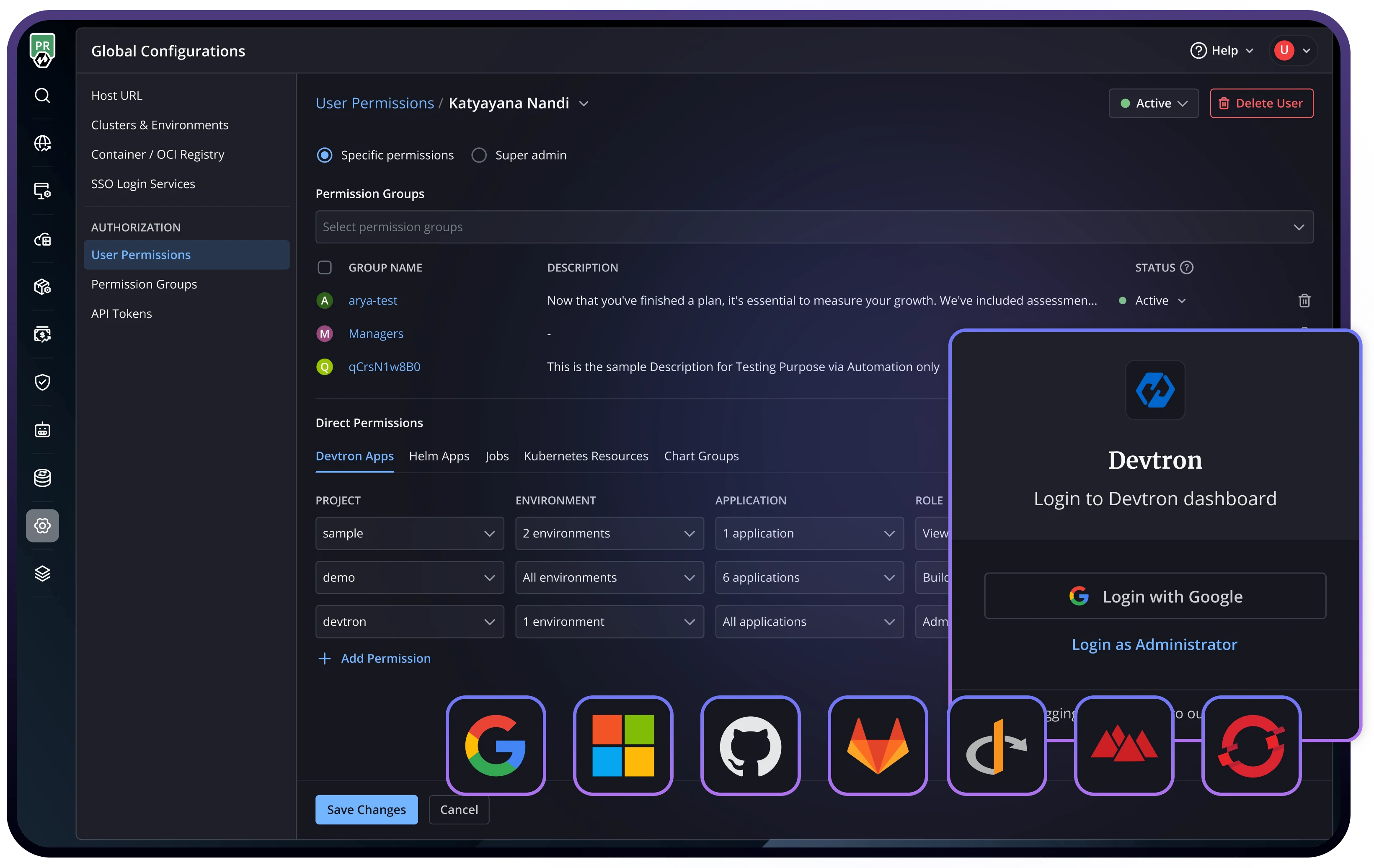
RBAC with break-glass procedures
Define precise permissions based on teams and responsibilities
Give the right people the right access, no more, no less.
Identity Management
Control access at cluster, namespace, and resource levels.
SSO Integration
Seamlessly plug in Okta, Keycloak, OIDC, and enterprise SSO.
Environment-Specific Permissions
Assign access based on deployment stage.
Audit Logs
Track every config change, deployment, and user action.
The
Free Plan That Actually
Covers What You Need
Access essential features without limits or hidden catches—start building with confidence at no cost.
Benefits of Using Devtron

Native integrations with your existing security and governance tools
No rip and replace required. Devtron enhances what you have.
The
Devtron
Difference
Discover how Devtron empowers teams to achieve DevOps excellence.
Read what our users have to say about their experience with our platform.
Frequently Asked Questions
Can we use our existing vulnerability scanners like Trivy or SonarQube with Devtron?
Absolutely. Devtron is designed to enhance, not replace, your current security tools. We provide native integrations with popular scanners, including Trivy, Clair, Docker Scout, SonarQube, and AWS Inspector. This means you can leverage your existing investments while gaining unified visibility and policy enforcement across all scanning results.
How granular can we get with RBAC permissions and policy enforcement?
Devtron offers multi-level access control that scales with your organization. You can set permissions at the cluster, namespace, application, and even specific resource levels. Policies can be configured globally and then customized for specific clusters, environments, or teams. Our break-glass procedures ensure emergency access is available while maintaining full audit trails.
How does Devtron handle secrets management and prevent secret exposure?
Devtron integrates with enterprise secret management solutions like HashiCorp Vault, AWS Secrets Manager, and External Secrets Operator. Our secret detection scans identify exposed secrets in code, configurations, and container images before deployment.
Can Devtron work in air-gapped or highly restricted environments?
Yes, Devtron supports air-gapped deployments and can operate in environments with strict network restrictions. Our platform can be deployed entirely within your infrastructure, with offline vulnerability databases and scanning capabilities. We also support custom registries and can work with existing security tools in isolated environments while maintaining full functionality.